Vulnerability Snapshot
This advisory is rated HIGH — exploitation is straightforward for a motivated attacker and impact is significant. Apply the vendor patch within your standard high-severity SLA.
Executive Summary
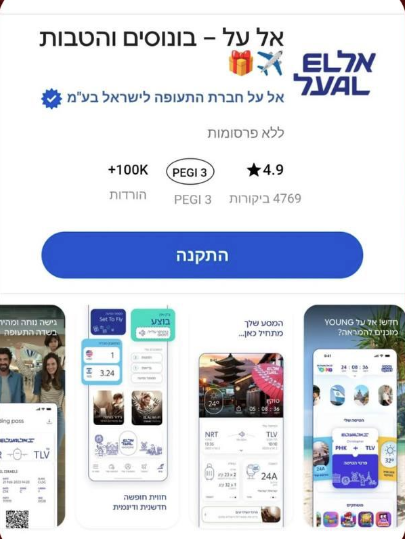
A new campaign is circulating online, impersonating the official El Al Israel Airlines mobile application and using sponsored-style ads to lure users into installing a fake app.
The ad presents a highly convincing interface, including:
* Official branding and logo
* App store-like layout (ratings, downloads, PEGI label)
* A prominent “Install” (התקנה) button
This creates a false sense of legitimacy and trust.
Attack Flow
* Download a malicious APK / profile
* Or enter personal and payment details
Indicators of Compromise (IOCs)
* Fake app distribution outside official stores
* Use of Hebrew UI mimicking trusted Israeli brands
* Overly generic install interface not tied to Google Play / App Store
* Suspicious hosting domains (not shown but implied from flow)
Key Risks
* Malware infection on mobile devices
* Credential theft (email, passwords, travel accounts)
* Financial fraud via stored payment methods
* Brand abuse is damaging trust in El Al
Why This Works
* High trust in national airline brand
* Familiar app store UI patterns
* Mobile users tend to act quickly without verifying the source
* Ads increase perceived legitimacy
Recommendations
For Users
* Only download apps from Google Play / Apple App Store
* Verify publisher name before installation
* Avoid clicking “Install” from ads or pop-ups
For Organizations
* Monitor for brand impersonation campaigns
* Work with platforms to remove malicious ads quickly
* Educate users about fake app distribution risks
AI Security Advisor
Powered by Gemini
Get AI-powered security recommendations tailored to this specific threat — including risk assessment, detection guidance, MITRE ATT&CK mapping, and actionable remediation steps.
Sources
Related Threat Alerts
- AI Agent Deletes PocketOS Production Database in 9 Seconds
- 🏴☠️ Lockbit5 has just published a new victim : bladex.com
- 🏴☠️ Lockbit5 has just published a new victim : studiopiu.net
- 🏴☠️ Lockbit5 has just published a new victim : bardehle.com
- 🏴☠️ Lockbit5 has just published a new victim : murni.co.id
- 🏴☠️ Lockbit5 has just published a new victim : heinrichs-logistic.de
Frequently Asked Questions
What is "Fake El Al App Ad Campaign Targets Users with Malicious Install Links"?
This is a high-severity threat update from an upstream security source. It covers the affected product family and was flagged for security teams to evaluate.
Am I affected?
Affected technology is listed in the Affected Products section above. If your asset inventory contains any of them, assume in-scope until you can prove otherwise.
How urgent is the response?
High: address inside your standard high-severity SLA (typically 7 days for internet-exposed assets, 30 days for internal). Skip ahead in the queue if the host is internet-facing.
How do I remediate?
Apply the vendor patch listed in the upstream advisory linked under Sources. If the patch is not yet available, follow the vendor-supplied workaround (often a config flag or feature disable) and add detections for the published exploit pattern in your SIEM. Re-scan after the patch lands to confirm the finding clears.
How does Vulnios help with this?
Vulnios continuously cross-references your asset inventory against the live CVE feed (NVD, vendor advisories, CISA KEV, and curated OSINT). When a new CVE matches your environment, you get a prioritized finding with the severity, KEV status, exploit-prediction (EPSS), and a direct path to the vendor patch. You can start a free scan from the homepage.
Protect Your Organization
Monitor CVEs, scan for vulnerabilities, and get real-time threat alerts — all in one platform.
Get instant alerts on Telegram
Join our public channel for real-time critical CVE alerts.
Follow @vulnios